The prevailing business landscape is rife with the threat of increasingly complex and sophisticated cyber-attacks, necessitating a shift in security approaches. Businesses need strategic vision and plan to strengthen the security systems and be future-ready.
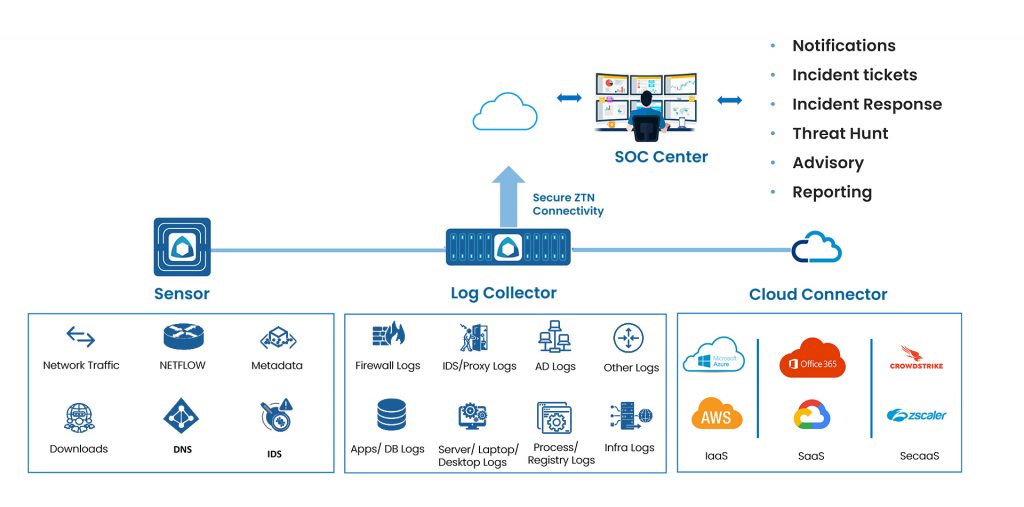
At MOURI Tech, our Security Operations Center (SOC) serves as the nerve center for enterprise cyber security. Here, a dedicated team of cyber security experts collaborates seamlessly with the clients, leveraging specialized skills to proactively monitor, identify, analyze, and respond swiftly to security incidents that could impact your organization’s digital infrastructure. By safeguarding critical data, our SOC ensures the resilience of your valuable information assets.
Here, a dedicated team of cyber security experts collaborates seamlessly with the clients, leveraging specialized skills to proactively monitor, identify, analyze, and respond swiftly to security incidents that could impact your organization’s digital infrastructure. By safeguarding critical data, our SOC ensures the resilience of your valuable information assets.




MOURI Tech’s Cyber Security team comprises a dedicated group of SMEs, extensively trained consultants, and seasoned professionals with global exposure across verticals. Connect with us to understand Cyber Security and compliance initiatives better and build robust mechanisms!
| Cookie | Duration | Description |
|---|---|---|
| cookielawinfo-checkbox-analytics | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Analytics". |
| cookielawinfo-checkbox-functional | 11 months | The cookie is set by GDPR cookie consent to record the user consent for the cookies in the category "Functional". |
| cookielawinfo-checkbox-necessary | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookies is used to store the user consent for the cookies in the category "Necessary". |
| cookielawinfo-checkbox-others | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Other. |
| cookielawinfo-checkbox-performance | 11 months | This cookie is set by GDPR Cookie Consent plugin. The cookie is used to store the user consent for the cookies in the category "Performance". |
| viewed_cookie_policy | 11 months | The cookie is set by the GDPR Cookie Consent plugin and is used to store whether or not user has consented to the use of cookies. It does not store any personal data. |